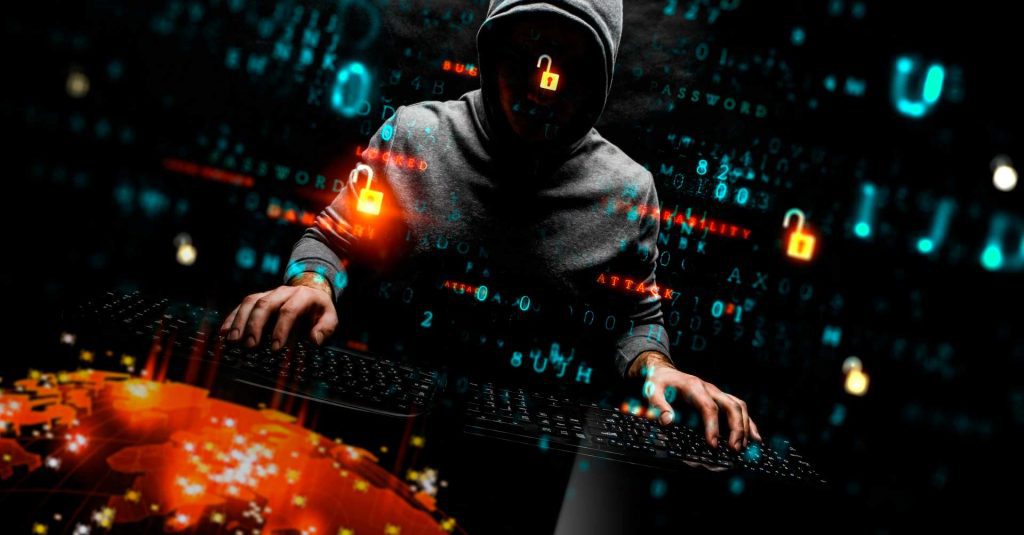
2020 has been a year marked by a virus, not one of the ones we usually talk about, but a biological one. COVID-19 monopolized people’s attention the past year, including among malware developers.
As we discussed in one of our posts, malware authors have used the pandemic to distribute rogue applications that were actually hiding malicious code to steal user data.
A large part of malware families, both banking and non-banking, have tried to take advantage of the health crisis through fraudulent campaigns in which their creations were distributed as if they were contacted tracing apps. Some of the families that have used this type of campaign are common knowledge, and we’ve talked about them before, as is the case with Cerberus.
Looking beyond the situation that’s appeared due to COVID-19, 2020 has been a year similar to 2019. New families of malware have appeared on both mobile devices and desktops, although as we expected, it appears that malware on mobile devices is on the rise. We say this because during 2020 we have seen the birth of three new families of banking malware for Android devices, while the families we are already familiar with, such as Cerberus and Anubis Bankbot, have remained among the most popular and active.
Even though malware for Android is growing, as we’ve previously mentioned, mainly due to the fact that all banking operations can now be carried out from mobile phones, ransomware has also continued to grow both on desktop systems and on mobile devices, but especially on desktop, mainly through attacks on companies to hijack and steal important documents.
This year, in addition to ransomware encrypting the victim’s files and asking for a ransom to give them back, it has also become fashionable for it to steal these files and ask the victim to pay extra in order to prevent the content of said files from being published, in a technique that has been dubbed doxing.
This new strategy is particularly successful in attacks on companies, which handle confidential customer information and don’t want this data to end up being published on the internet.
In short, 2020 has been the year of Android banking malware and desktop ransomware, and in 2021 this trend is expected to continue, as ransomware is the malware that reaps the most benefits while also being the simplest to develop.
Below are the most interesting and newest malware families that 2020 has given us.
Submitted by buguroo